Until not long ago, I didn’t think twice about sharing my old (then main) Gmail email address with literally any and every service I’d come across in the internet.
A 10% discount for sharing my email with this questionable eCommerce site? Sure, why not.
Signing up to a dodgy forum just to be able to read some obscure post from 7 years ago? Hell yeah!
I never really thought of my email address as sensitive information. Sure, I may get newsletters that I can unsuscribe from, or perhaps some annoying marketing or sales emails here and there, but most of the crap was already filtered out by Gmail and sent directly to Spam, so I thought that was about it, no harm done.

Unfortunately, spam, phishing and annoying unrequested newsletters are not the only danger you face when you share your email address. Today, when you sign up for a website, app or service, other than your name or alias and other personal details, you’ll also be asked for your email address. And funny enough, there can be more than one person in the world with the exact same full name, but there can only be one person with a certain email address. Our email addresses are exclusively unique to ourselves. And by sharing the same email address with all these services, we would essentially turn that email address into our main online identity, our alias, our username. This raises both security and privacy concerns.
By using the same email address for all our services, anybody who knows our email address will already know half (or one third if you use 2FA 😉 ) of the required details for signing into literally any of our accounts – This includes banks, social media accounts and many more services with yet more sensitive information you’d probably not want anybody to see (like Uber Eats and your shameful track record of pizza and falafels ordered since the pandemic started, huh?)

But sure, even if a bad actor get their hands on our email address, they would still need to figure out our password, right?
Breach data
As we all know, vulnerabilities are discovered and exploited all the time. Systems will be attacked, data will be breached, and personal sensitive information will be exposed. This sad reality is just part of the era we live in. And if you reuse your password for multiple sites, this also means your accounts can (and will) be compromised.
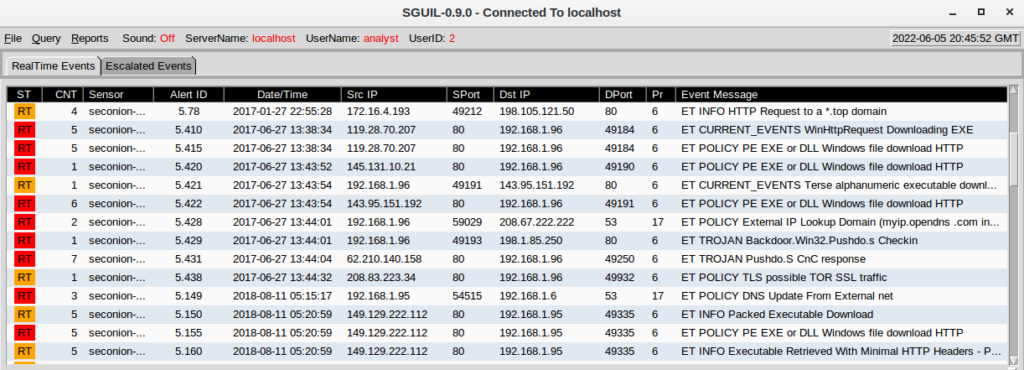
Taking for example a random email address (censored for obvious reasons), we can see through a quick search in Haveibeenpwned that there have been at least 11 different data breaches containing details about this specific person, some of which may include passwords too:

The information pertaining these breaches is often sold (or even shared for free) in the dark web. These 11 breaches are just the ones that have been disclosed with the Haveibeenpwned service, but there could be some additional undisclosed breaches. Additionally, there are countless resources in the clearweb that compile breach data, allowing anybody to search for a specific email, phone number or alias and find what type of information has been exposed about that profile. One of these sites is Breach Directory.
If we search for that same email address in Breachdirectory, we can see there’s 3 partially exposed passwords for this email address, alongside their SHA-1 hash:
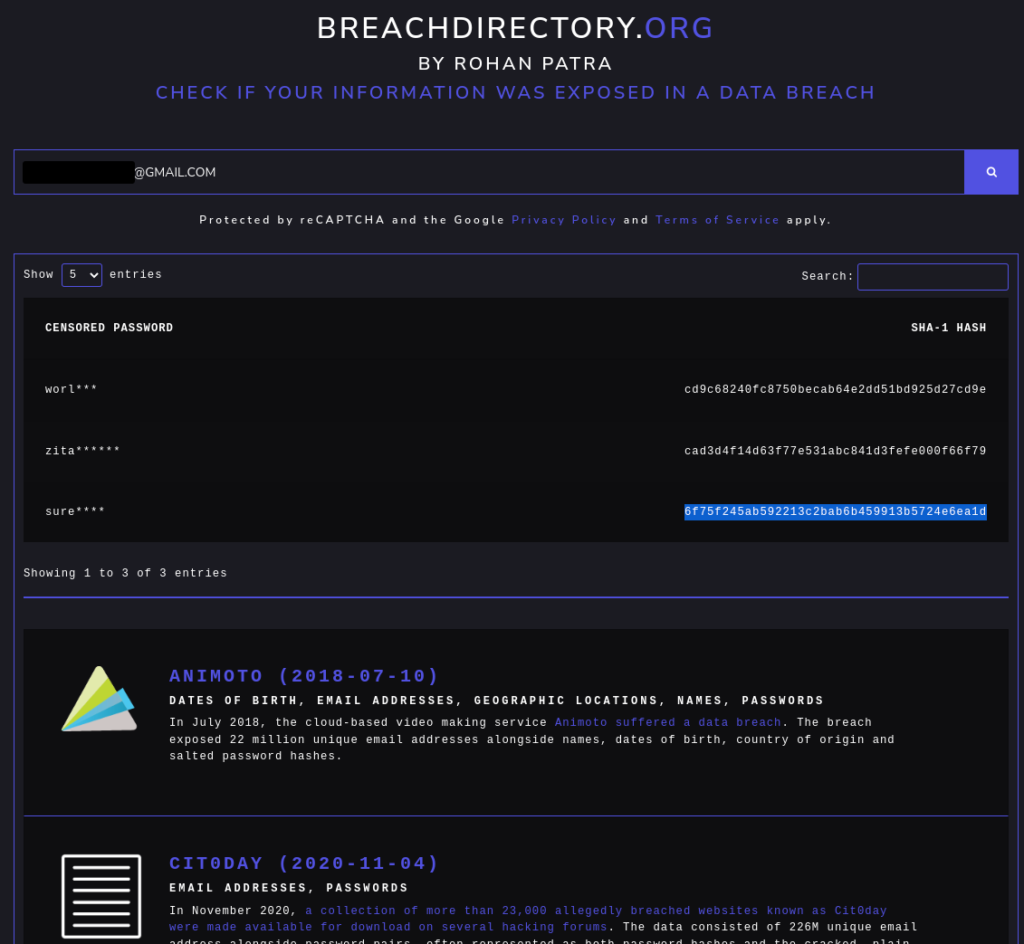
It’s very rare (but unfortunately still possible) for a site to store their user’s passwords in plain text today. Most often, when an adversary gains access to a system and obtains user records, they would not get the user passwords in plain text but instead, the passwords would be hashed as a long string of alphanumeric characters and symbols. The possibility to decypher these hashes depends on how strong the encryption used to hash them is, as well as whether they may have been salted and peppered. However, many sites still encrypt their users passwords as SHA-1, a weak and deprecated/advised against encryption algorithm that can be easily cracked.
In the screenshot above, we can see how these censored passwords also include their SHA-1 hash. However, SHA-1 can be easily cracked in a matter of seconds using tools like CrackStation:

And voila! If this user reused any of these passwords for any other services, this would mean any bad actor could now pivot and take over any additional accounts with those same usernames and passwords, accessing yet more private and personal information.
This scenario is just a quick example of one of the most common ways a password can be compromised, but there are certainly many more. To avoid this, there are three very important rules of thumb to follow:
- Use long, complex passwords or passphrases.
- Never reuse passwords across multiple sites.
- Enable multi-factor authentication when possible (and preferably with an authenticator device or app instead of text or phone verification).
- And of course, use email aliases so that even if one of your accounts ends up being breached, it won’t be tracked back to you or your other accounts.
Email aliases
Other than the security concerns of data breaches, there are also many privacy concerns about how and who to share your email address with. Your email address can be cross-checked with many other services or social media, allowing anybody who knows your email address to search your profiles or try to access any additional information about yourself.
Before I share my email with any service or website, I generally ask myself some questions; “How much do I trust this site? How do I know this site will not sell my data? Am I sharing any other personal information with this site?“. It is important to understand your threat model and how comfortable you feel about sharing personal information.
There are many different processes you can use to reduce the fingerprint of your email address, either through forwarders, aliases or disposable, temporary email addresses, taking control over who you share it with, and it all would depend on your own threat model. In my case, I’d generally consider 4 different categories or use cases:
1. One-time access sites / Unimportant sites
There are many websites that will require you to sign up and validate an email address before continuing through the website (ie blocking part of a news article or hiding a download page behind a sign up wall).
Generally, if I believe the website or service is not important nor am I sharing any other personal details, I wouldn’t want to share any email address that can be linked back to me. This would generally be the case for websites with a dubious or unknown reputation, or that I’ll probably not need to access more than once or twice. For these type of scenarios, I generally use disposable email services like Guerrillamail and TempMail. These type of services will provide a randomly generated email address and access to its inbox for a limited period of time, allowing you to receive any one-time access codes or authentication URLs to finish the registration process. It is important to note that generally, email addresses generated through these services can’t be retrieved after a limited time, so your access to these mailboxes would be limited to a very short period of time.
2. Newsletters, low-importance sites and publicly available email addresses
When signing up for newsletters, registering for forums or seting up certain alerts, I’d expect to receive emails from these services periodically. In scenarios like these where I generally don’t share any other personal information, I’d use an email forwarder instead. This is also the case of when I want to offer an email address publicly (like in the home page of prats.co) that end up appearing in search engines and scanned by web crawlers.
For scenarios like this where no sensitive information will be sent across, I generally use third party email forwarders. There are many providers that offer free email forwarding, including:
- AnonAddy: Offers free and paid plans. The free plan includes unlimited email aliases but a limited bandwitdth. AnonAddy is open source and allows you to bring your own GPG/OpenPGP public keys.
- SimpleLogin: Offers free and paid plans. The free plan is limited to 10 email aliases, but has unlimited bandwidth. It is also open source and also allows the option to bring your own GPG/OpenPGP public keys. SimpleLogin has recently been acquired by ProtonMail.
- Duckduckgo Email Protection – Free service included in their browser app and browser extension. Allows you to create a main alias ([email protected]), as well as unlimited, randomly generated aliases. There doesn’t seem to be any set limits in bandwidth. This service will also automatically remove any email trackers for enhanced privacy.
The main benefit of third party email forwarders is that you can disable or delete the alias at any point, which would stop any emails sent to that address to ever be forwarded to your inbox. So if any of the services where you registered an account with an email alias gets compromised, you can simply disable that alias and your real email would never be exposed.
There are many similar services like Firefox Relay or 33mail, but I’ve not tested these long enough to be able to recommend them yet!
3. Important services and accounts
Although third party email forwarders are an excellent option, when it comes to important services and accounts I prefer to be fully in control. Thinking of a worst case scenario, it is possible that any of these email forwarders may suffer any incident that could limit their functionality. Or maybe my account with them can be compromised, cancelled or disabled. If my most important emails and accounts are set up under a domain which I no longer have full access to, this could cause a lot of trouble.
Following this approach, I use my own aliases (ie randomtext@prats.co) for important accounts that would still have some of my personal information anyway, specially accounts with payment information, full name and home address. To do this, I would just simply need to set up a catch-all address in my email provider, which would allow any email sent to my domain, even if the address does not exist, to be delivered to a default catch-all inbox. This also guarantees that, for as long as I have access to the domain, I’d be able to migrate to different email servers and maintain these aliases as long as the new email server offers catch-all addresses as well.
Enabling a catch-all address is also a good way to prevent most forms of email directory harvest attacks, where bad actors would try to validate whether an email address exists or not for a certain domain by delivering bulk emails and analyzing the email server response (delivered, blocked, not found, etc).
An alternative way to set up aliases for your main domain is through the +Aliases option. Some email providers offer this feature, allowing you to create unlimited aliases for your main email address by just adding a + after your name (for example [email protected]). This is of course not as effective as catch-all aliaes as it would still expose your main email address, but this feature is available for free services without requiring a custom domain, so you could use +Aliases if you’re still using Gmail, or with a free Protonmail account.
When using aliases under my domains, I generally set up aliases directly related to the service they’ll be used in, but salted (so that they wouldn’t be that easy to guess). So for example, if I’m setting an email alias for Amazon, I could add extra numbers or words to the name Amazon, so instead of using [email protected], I could use [email protected] or [email protected].
4. Friends and family
Lastly, I only use my real email addresses with friends and family. I avoid using these addresses for any online portal at all, and only use them to communicate with people I trust.
Of course, following the steps of this article would result in endless, unique passwords and email aliases for each service we use. And as that is humanly impossible, you should consider using a password manager if you’re not using one already. They are super easy to use, easy to set up and it is honestly one of the biggest improvements I’ve ever taken regarding security hygiene and account management. For personal use, I highly recommend using Bitwarden – It is free, open source, has been privately audited multiple times and it can also generate email aliases through AnonAddy and SimpleLogin APIs.
Additionally, please note some services like Have I been Pwned and Breach directory offer the ability to delete breached data upon request. If your information has been exposed, you can request its removal here:
- Have I Been Pwned – Opt Out – https://haveibeenpwned.com/OptOut
- Breach Directoy – Delete my data – https://breachdirectory.org/deletemydata