Through my learning in the CyberOps certificate through The Open University, what I really enjoyed the most were the hands-on labs, specifically the forensic investigation ones, as that’s where I could practice all the theory learnt thorough the course. These labs did not only focus on Cisco proprietary software, but also provided brilliant instructions and labs for many open-source IDS and IPS services which is always great! These forensic labs would often be hosted in a Security Onion VM, and would often have us scanning through existing alerts in multiple IDS systems like Sguil, Wireshark, Zeek (Formerly Bro), Kibana and NetworkMiner, with the goal of trying to identify the first signs of infection of real-life threats.
At the end of this certification, after passing the Cisco CyberOps exam, The Open University also required to complete and report a cybersecurity investigation using all the tools available in Security Onion. This investigation consisted on the analysis of a machine infected with the Pushdo trojan. The samples and VM for this investigation were obtained from malware-traffic-analysis.net, as per the Cisco documentation.
Now that the submission period for this assesment is over, I wanted to share the details of this forensic investigation as I think it is a very interesting resource for anybody considering taking this certification. If you are considering taking this course, or are already enrolled in it, please use this article as a reference only and don’t copy any of the contents of this post – Where’s the fun in cheating? 😉
This assignment consisted of 4 steps (First one is unmarked), and it counted for up to 30% of the final assessment mark:
Step 1: Verify the status of services (unmarked)
A – Log into Security Onion VM using with the username redacted and password redacted.
B – Open a terminal window. Enter the sudo so-status command to verify that all the services are ready.
C – When the nsm service is ready, log into Sguil or Kibana with the username redacted and password redacted.
Step 2: Gather basic information
A – Identify the time frame of the Pushdo trojan attack, including the date and approximate timespan:
2017-06-27 from 13:38:34 to 13:44:32
B – List the alerts noted during the time frame associated with this trojan:
Identified by the name Pushdo in alert 5.429, event message ET TROJAN Backdoor.Win32.Pushdo.s Checkin. Full list of alerts noted during this time:

C – List the range of internal IP addresses and external IP addresses involved:
We can see the attack starts with alerts ID 5.410 and 5.415, where the source IP address 119.28.70.207 (external) reaches out to the destination IP address 192.168.1.96 (internal).
Other than these 2 IP addresses, in the subsequent alerts we can see that there are additional external IP addresses communicating with the internal IP address 192.168.1.96. The full list of IPs involved in this attack are (in order of appearance):
- 119.28.70.207 (External)
- 192.168.1.96 (Internal)
- 145.131.10.21 (External)
- 143.95.151.192 (External)
- 208.67.222.222 (External)
- 198.1.85.250 (External)
- 62.210.140.158 (External)
- 208.83.223.34 (External)
Step 3: Infected host
A – Based on the alerts, what is the IP and MAC addresses of the infected computer? Based on the MAC address, what is the vendor of the NIC chipset?
Infected computer IP address: 192.168.1.96
Infected computer MAC address: 00-15-C5-DE-C7-3B
NIC Vendor: Dell Inc.
Details found in NetworkMiner by, in Sguil, right-clicking on alert ID 5.410 and then clicking on NetworkMiner > Expand on 192.168.1.96

Additionally, the 3 first pairs of numbers of the MAC address (in this case 00-15-C5) are generally reserved to a specific vendor and can easily be found via any search engine.
B – Based on the alerts, when (date and time in UTC) and how was the system infected?
In NetworkMiner, in the Files tab, we can see a file was downloaded from a website (with source host 119.28.70.207) to the user’s Windows computer (192.168.1.96) at 13.38.32 UTC on the 27th of June, 2017:
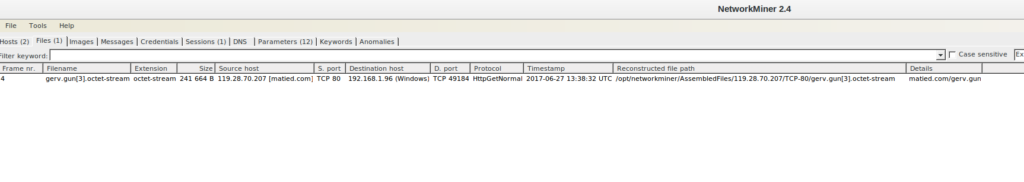
Only two seconds later, the first alert of this infection was created in Sguil, at 13.38.34 UTC.
The system was infected via the download of a malicious file. The user downloaded the file gerv.gun through the malicious site matied[.]com. We can generate a MD5 hash of this file through NetworkMiner (1568dafae63eebce20987dd6205704e5), and search it in Virustotal.com. This search shows the file has a malicious score of 59/68:
https://www.virustotal.com/gui/file/0931537889c35226d00ed26962ecacb140521394279eb2ade7e9d2afcf1a7272
C – How did the malware infect the system?
Shortly after downloading the gerv.gun file, we can see in alert 5.429 a potential trojan alert (ET TROJAN puBackdoor.Wind32.Pushdo.s Checkin). Pushdo is a malware distribution system, also known as a “downloader” trojan. Its purpose is to, once executed, download additional malware to the infected host.
Once infected with Pushdo, the host will reach out to additional external hosts/IP addresses and will download additional malware. When executing the file, Pushdo will reach out to one of the C2 (Command and control) server IP addressed embedded in its code. These requests are done via HTTP, which might work as an extra layer on its evasion method, camouflaging within real HTTP packets.

Pushdo would then proceed to infect a computer with additional malware, which could inject many sorts of different payloads. The malware that will be downloaded by Pushdo depends on the “Version” value, at the beginning of this GET request.
Step 4: Examine the exploit
A – Based on the alerts associated with HTTP GET request, what files were downloaded?
B – List the malicious domains observed and the files downloaded.
Answering questions A and B together:
By searching the range of alerts of this incident in Wireshark, and then applying the http filter, we can see the following files were downloaded through HTTP GET requests:
- gerv.gun – from matied[.]com (119.28.70.207)

- trow.exe – from lounge-haarstudio[.]nl (145.131.10.21)

- wp.exe – from vantagepointtechnologies[.]com (143.95.151.192)

Additionally, after downloading the 3 files, we see the malware communicating to additional domains, potentially a C2 server sharing additional instructions on what the infected machine should do. The additional domains are:
- www.sjbs[.]org
- www.tyrns[.]com
After this, we see in the last alert (5.438) an encrypted transcript, identified as possible TOR SSL Traffic, with calls to stranger/scrambled domains:
- www.kid67ap2i5b5d4ekvcg[.]com
- www.xfbploco2q[.]com
- www.6acbzspvq[.]net

C – Use any available tools in Security Onion VM, determine and record the SHA256 hash for the downloaded files that probably infected the computer?
gerv.gun SHA256: 0931537889c35226d00ed26962ecacb140521394279eb2ade7e9d2afcf1a7272
trow.exe SHA256: 94a0a09ee6a21526ac34d41eabf4ba603e9a30c26e6a1dc072ff45749dfb1fe1
wp.exe SHA256: 79d503165d32176842fe386d96c04fb70f6ce1c8a485837957849297e625ea48
I obtained the SHA256 hash for the files through Network miner. In the files tab, right click on each of the downloaded files and selected “Calculate MD5 / SHA1 / SHA256 hash”:

D – Navigate to www.virustotal.com input the SHA256 hash to determine if these were detected as malicious files. Record your findings, such as file type and size, other names, and target machine. You may also include any relevant information provided by the community as posted in VirusTotal.
- gerv.gun
- 59/68 security vendors flagged this file as malicious
- File type: Win32 EXE
- File size: 236.00 KB (241664 bytes)
- Other names: test, tmp523799.697, tmp246975.343, tmp213582.420, extract-1498570714.111294-HTTP-FG0jno3bJLiIzR4hrh.exe, 0931537889c35226d00ed26962ecacb140521394279eb2ade7e9d2afcf1a7272.bin, vector.tui
- Target machine: Intel 386 or later processors and compatible processors
- trow.exe
- 58/67 security vendors and 1 sandbox flagged this file as malicious
- File type: Win32 EXE
- File size: 323.00 KB (330752 bytes)
- Other names: taswexuahoft.exe, Pedals , Pedals.exe, trow.exe, test3, 2017-06-28_18-18-14.exe, bma2beo4.exe
- Target machine: Intel 386 or later processors and compatible processors
- wp.exe
- 57/68 security vendors flagged this file as malicious
- File type: Win32 EXE
- File size: 300.50KB (307712 bytes)
- Other names: wp.exe, 8lmwzz8vu.dll, test2, test_3, 4da48f6423d5f7d75de281a674c2e620.virobj, wp.exe.x-msdownload
- Target machine: Intel 386 or later processors and compatible processors
There was no additional/relevant information in the VirusTotal community for these files that has not already been listed here, and most comments were links to external blogs.
E – Evaluate other significant alerts associated with the infected host during this time-frame and record these
In alert 5.428 (Message: ET POLICY External IP Lookup Domain myip.opendns .com in DNS lookup), we see the infected host is communicating with the destination IP 208.67.222.222 through the destination port 53 (DNS). Opening this alert in Wireshark, we can see two packets which look like a DNS lookup:
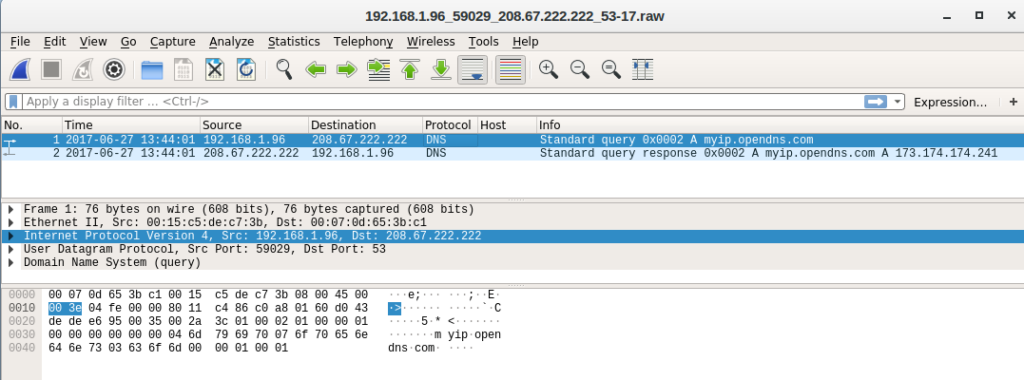
This DNS lookup (alert 5.428) occurred at the exact moment of the Pushdo infection alert, 13:44:01 UTC. This is the moment the infection started.
As I completed this course via The Open University, the deadline for submission for this assessment (as part of the final assignment, which also consisted on a final exam and an essay) is today, 6th of June at 12PM BST, hence why I wanted to wait until the deadline passed to post this article.





